Blog Archives
Instagram Stores Geolocation Data in EVERY Photo without Users Knowledge

If Instagram asks you if it can use your current location, even only once, it will autmacticly store the locaction of EVERY photo taken, even though it didn’t tell you that it would do that! There is no setting to only use this for certain photos. The location wont be publicly visible (unless you select it to before you publish the photo), but it will be publicly available….
The scary thing is that this is not hard to get. All you have to do is go to ink361.com and sign in with your instagram account. Once you’ve signed in you can view all of your (and people you follow) photos. If you click on a photo it will have a little map at the botom which will tell you where the photo was taken.
Requirements
An Instagram account
Instagram is Allowed to Use Your Location (Check settings)
A Computer to Access ink361.com
Instructions
1. Go to ink361.com and sign in with your instagram account.
2. Once you’ve logged in you need to find a photo you want to geolocate. I am going to find the location of a photo on the popular page. Scroll to the bottom of the photo and you will see a little map. You can click on that map to see where the photo was taken. This does not give you an address or coordinates though, and it is hard to see street names. If you would like to see the coordinates read below.
Finding the Coordinates
1. You will need Chrome (you can do it with other browsers though). Right click on the little map and click “Inspect Element”
2. Now you should see a clump of text highlighted in blue. The coordinates will be after the part:
size:small%7C
It will be directly after the 7C
3. Now that you have the coordinates head over to Google Maps and paste the coordinates to see the address!
UPDATE: There is an easier way to find the coordinates. Go to the website http://hashgr.am/ It will give you the option to search for a user or just search instagram. Put in the user you want, click on the photo you want….And volla, the coordinates will be at the bottom of the page with a link to google maps!
Also you don’t have to be an instagram user to do this!!!
View All of the User’s Photos on a Map
1. If you would like to see all of the user’s photos on a map at once follow the instructions in the pics below
How to turn this Off
If you would like to have Instragm stop geotagging all of you photos just go into your Settings and un-allow instgram to use your location. The downside to this is that if you want to use the actual geolcation feature (the one that lets people see the location of the photo inside the actual app) You would have to re-allow instagram to use your location (and turn it off again when done). That could be a very time consuming process.
This can be scary because if you take a photo at your house, you probably didn’t relize that people now know the address of your house. Say you had a lot of followers, maybe one of them is………a stalker -_-
Crack: WPA & WPA2 Passwords in 4-10 Hours!
WPA & WPA2 used to be impossible to crack unless you used brute force. Back in Febuary, a Linux program called Reaver came that exploits a flaw in WPS (Wifi Protected Setup). This attack takes anywhere from 4-10 hours (the closer the faster). When I tried it took 8 hours. Other people have had it happen in 2!
Requirements
Backtrack 5 Live CD
Reaver
Almost any Computer
Instructions
1. First off you will need to create a Backtrack 5 Live CD.
NOTE: A live CD is a bootable operating system that can run on any computer. Don’t worry, it won’t delete your current operating system and NOTHING will be changed. The Live CD will temporarily store the things you download to your RAM (Random Access Memory). Once you shut down the computer, everything you installed (on the live CD OS) will be deleted. And you current OS (Operating System) will be back with everything unchaged.
Head over to the Backtrack Download Page and select Bacaktrack 5 R1 > GNOME > 32 > ISO > DIRECT

Once its downloaded you need to burn the ISO to a CD.
NOTE: I will show you how to do this on a MAC but its pretty easy to do on a windows.
Open up Disk Utility. Its in the folder /Applications/Utilities/
Drag Backtrack 5 into Disk Utility, select it, and click on burn
Insert your blank CD or DVD and burn it (If it fails try burning at a lower speed).
2. Once you have Backtrack on a CD/DVD insert it in your computer and shut it down. If you are on a mac start up your computer while holding down “C” without the quotes.
If you are on a Windows you need to change your BIOS settings to start up from a CD.

3. It will take a little time to boot into Backtrack. Once you’ve reached the prompt, type startx
4. Right now, Reaver is not incorporated into the live CD. So you will have to install it. So you have to have access to a wifi network to download reaver, then you can crack any network!
Click Applications > Internet > Wicd Network Manager
Click on the network you want to connect to download reaver (not the one you want to crack).
Now that your connected to the internet, its time to install Reaver!
Open up terminal Applications > Accessories > Terminal
At the Prompt, type:
apt-get update
After the update type:
apt-get install reaver
Reaver should be installed now!
5. You need to find out your wireless card, in terminal type:
iwconfig
Your card most likely will be named wlan0. But it could be called something else, you will need to determine this on your own.
Now we will put your card into monitor mode! Type:
airmon-ng start wlan0
NOTE: I am assuming that your wireless card is wlan0, if it is not replace wlan0 with your wireless card!
Now you need to get the BSSID of the router you want to crack. To do this type:
airodump-ng wlan0
If wlan0 doesn’t work try mon0
You will start to see wireless networks show up. Once the one you want to crack is on your screen, click Ctrl+C
Copy the BSSID down on notepad or a piece of papper.
6. Now you are going to start using reaver! Replace moniterface and BSSID with the BSSID and the monitor interface you copied above!
reaver -i moninterface -b bssid -vv
Reaver will start preforming its creepy magic! It will try a bunch of different WPS pins (Wifi Protected Setup) to determine your password!
How to Protect Yourself against Reaver?
You can protect yourself by turning off WPS in your routers settings. This doesn’t always work though. Or you can install DD-WRT which is a new firmware for you router that gives it TONS of new features, and…it doesn’t support WPS. So you will be protected xD
Bypass: Login Screens on Forums that make you Join to View their Content
If you’ve ever been to a forum that requires you to join to view their content there is a way around the login screen. And its VERY simple!
Most forums still let google index their site. So all you have to do is change your user-agent to Google Bot! Once your user agent is spoofed, the site will think you are Google and let you view the page!
Requirements
Firefox (You can do this with any browser but I am using firefox because its the easiest)
User Agent Switcher for Firefox
Instructions
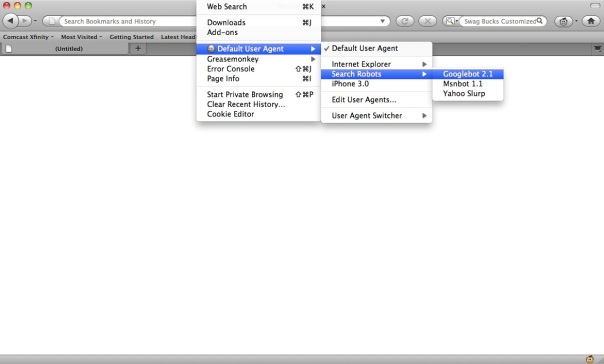
Once You’ve installed User Agent Switcher all you have to do is navigate to Tools > Default User Agent > Search Robots > and Click on GoogleBot 2.1
Now just clear your cookies and head back over to the forum you want to view!
You can do this on any browser. Firefox is the easiest though because it has the GoogleBot User Agent built in. On another browser you would have to add a the user agent string.
The User Agent string for GoogleBot is:
Googlebot/2.1 (+http://www.googlebot.com/bot.html)
Hack Your Way: into a Yahoo Account!
There are a few ways to hack into peoples accounts. I’m going to cover man in the middle attacks.
Here is a description of a Man in the middle attack from wikipedia:
“The man-in-the middle attack intercepts a communication between two systems. For example, in an http transaction the target is the TCP connection between client and server. Using different techniques, the attacker splits the original TCP connection into 2 new connections, one between the client and the attacker and the other between the attacker and the server, as shown in figure 1. Once the TCP connection is intercepted, the attacker acts as a proxy, being able to read, insert and modify the data in the intercepted communication.”
Theses kind of attacks are scary because anyone can easily get into your accounts as long as they are on the same wifi network as you (Public Hotspots such as Starbucks). This attack only works on sites that don’t use HTTPS encryption. The scary thing though is that Yahoo STILL DOESN’T use it! Facebook and Gmail do! This method works on most sites though because they don’t offer HTTPS encryption.
To accomplish this attack you need a application to sniff a network for packets. The best applicaction for this would be Wireshark. Wireshark is free, works on Windows, Mac, & Linux, and is open source! Also, you must be on the same network as the person you want to hack.
Requirents
A Computer
Wireshark (Free)
Firefox 3.6.12 (Older Version required for firesheep)
Firesheep (Optional but helps)
Instructions
Note: I am using a Mac, but these instructions can be done on any computer.
1. In the following picture I am going to show you how to start sniffing the network for packets.
2. Once you’ve started the capture, you will see a bunch of packets beign displayed. We need filter the packets out. I am hacking into a yahoo account but the instructions are basically the same for any account. In the filter tab type:
http.cookie contains “yahoo”
You would replace “yahoo” with the website you are hacking into.
3. Now you need to wait until the victim access the site. Once they acces it you will see green things on your screen. Select the latest one and right click on [truncated ] Cookie, and select copy < Value
4. Now open up a word prosecor (Text Edit, Notepad, etc) right click and cick paste. Now there will be a bunch of random charicters on your screen. For Yahoo the authentication cookies are named “Y” and “T”. Here is a sample of the cookies:
Y=v=4&h=k6ehjga7k8d4h/o&p=f766666&r=36&lg=enS&intldg=WTLd5pEjTEWqmQn6DP7jhVwL7AomjJKyQzAnAT5ywDsHUdDFYL; T=dhNUDeLUwrXt38BtFHdmdjEJ 5E4M94SfKFzpJ&7ADCP3A59ujhR- KPaqKwYFECFnYuifEn5fdQ2G5EbkntiCVeQhBy4LSzPAzM43oGB3S2pffSWDPkagLTPEFV6jU8zZXiWHjH yXgJ8FbxMZhiT4FvTBtrS6v4QjP57fUtqX5Tp4cxmUyDMLdJeNusUazAUoT57RRvDtdThRc92cobJ3Md58 Lhw9yR–
I bet your wandering how to tell the cookies apart. Well the start of a cookie will be the name with and equal sign after it. Everything after that is the contents of the cookie. Once you get to a semicolon with a space after it, the cookie is over, and a new one begins!
In the picture above I have highlighted the to necasary cookeis.
5. Once you’ve got the authenticaciton cookies, you need to open up Add n Edit Cookies in Firefox. Clear all of your cookies first and then click add a cookie
Start with either the Y cookie or the T cookie. I’m going to start with the Y. Fill in the name as Y, the content as the part after the equal sign, the path as / and the host as .yahoo.com
Almost any site you want to hack the host would be the url with a period in front of it.
Do the same thing for the T cookie.
Now type in your address bar yahoo.com/mail
You have successfully hacked into your victims account!
TIP: Firesheep is a simplified version of this and automates it all. But it doesn’t work for very many sites anymore. But it is useful to find out the authentication cookies (So you don’t have to enter EVERY single cookie)
Hack Your Way: to Free Internet!


MAC spoofing is easy! And you can do it on any operating system. We are going to use it to get free internet at paid hotspots. Wireless routers identify users by their MAC addresses. If you spoof someone else’s MAC address that has already paid, you will get free internet to! This works best when you are at a hotel, or somewhere where people aren’t always using their computers because two MAC address cant be on the same network at the same time.
Requirements
A Computer
A Network Scanner (I use iNet for Mac)
Instructions
NOTE: I will be using a Mac, but these instructions can easily be done on any computer.
1. First learn how to spoof your MAC address.
CLICK HERE FOR WINDOWS (You can use any software this is just one of many!)
2. Log onto the network you want free internet. After you are on the correct network you need to scan it for MAC Address. To scan on Mac I would recommend iNet. On windows use this. Make note of all of them. A couple hours later scan again. Note which ones aren’t there anymore. I like iNet because it does this for you. iNet is also available on the iPhone and is FREE!
3. Now pick one of the ones that was offline and use that MAC address as your spoofed address. Log back onto the network and you should have free internet. If you don’t that person hasn’t paid and you need to try a different offline MAC address.
Things you need to think about before you do this.
1st of all, if the hotspot charges you by the amount of hours/minutes you use it, you are charging THEM extra. Also if they try to connect to the network and you are using it, they won’t be able to connect.
Hack Your Way: Free Background Checks on the iPhone (Update)

The background checking service BeenVerified is normally paid. And you also have to set up an account. But their iPhone app gives you 1 free credit to try out their service. But it verifies your a new custamer with your UUID, which can EASILY be spoofed!
Requirements
BeenVerified iPhone App (Free)
UDID Faker ( from the xsellize repo “cydia.xsellize.com” without the quotes)
Instructions
1. Open up BeenVerified and use your 1st free credit (You don’t have to make an account). Once you’ve used your free credit exit the app and delete it from your multitasking bar. Open up UDID Faker and select BeenVerified and change your UUID! Now open back up BeenVerified and use your free credit again.
UPDATE: Now you have to make an account to use the credit. But thats not really a problem, because you could just put a fake email and password (they don’t send a verification email). This is actually a bonus, because you can go online and sign in with your “fake” account and use your credit online (which has a little more options).
Your old searches won’t be on there anymore. But before you change your UUID you can email yourself a copy of the Background report from the app!
I hope you enjoyed the tutorial!
CHECK OUT THIS POST! “Hack: White Pages for Free Reverse Cell Phone!”











![Yahoo [HACKED] !](https://hackerue.wordpress.com/wp-content/uploads/2012/03/yahoo-hacked.png?w=604)










